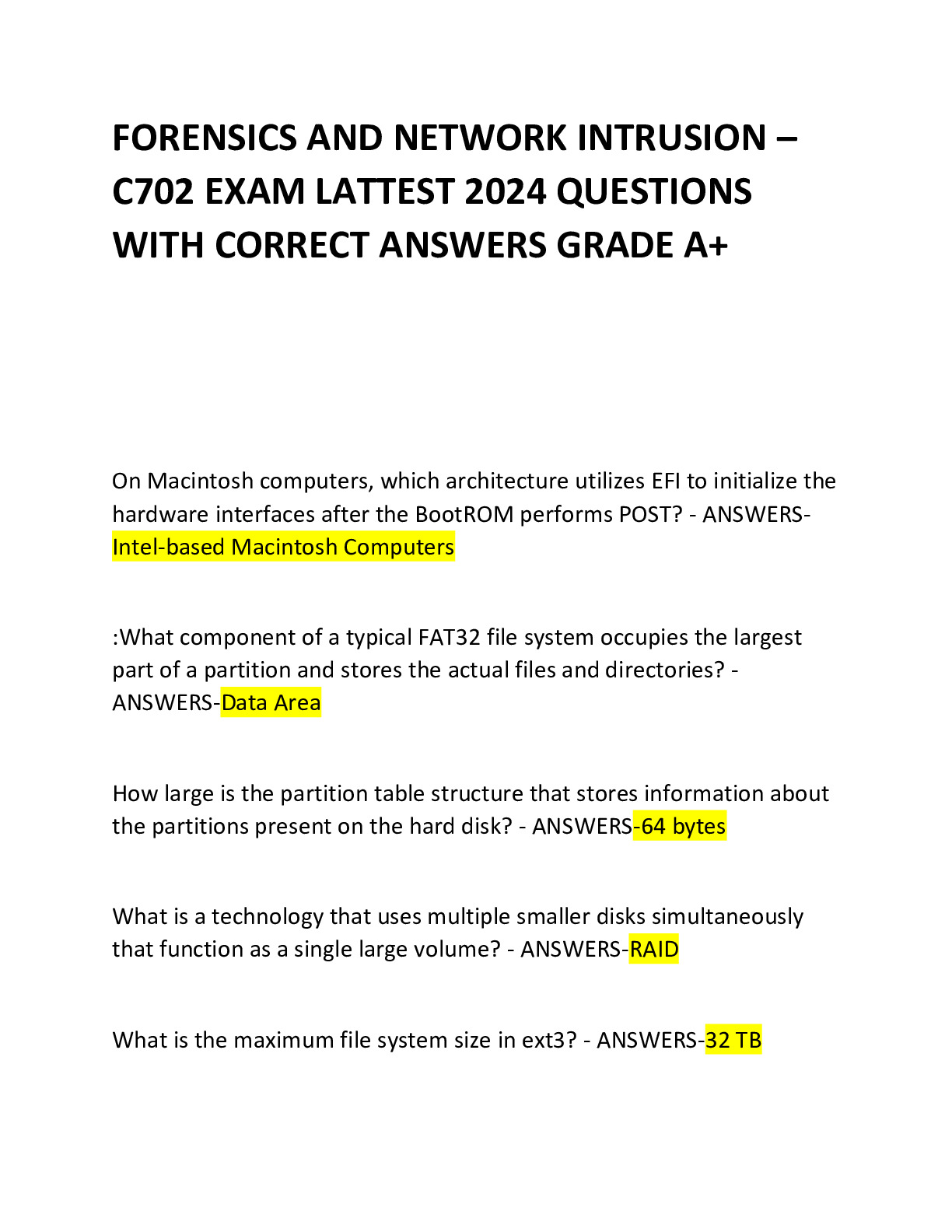
How large is the partition table structure that stores information about the partitions present on the hard disk?
64 bytes
On Macintosh computers,
... [Show More] which architecture utilizes EFI to initialize the hardware interfaces after the BootROM performs POST?
Intel-based Macintosh Computers
:What component of a typical FAT32 file system occupies the largest part of a partition and stores the actual files and directories?
Data Area
What is a technology that uses multiple smaller disks simultaneously that function as a single large volume?
RAID
What is the maximum file system size in ext3?
32 TB
What is the maximum file system size in ext4?
1 EiB
:What layer of web application architecture is responsible for the core functioning of the system and includes logic and applications, such as .NET, used by developers to build websites according to client requirements?
business layer
What stage of the Linux boot process includes the task of loading the virtual root file system created by the initrd image and executes the Linuxrc program?
Kernel Stage
What UFS file system part comprises a collection, including a header with statistics and free lists, a number of inodes containing file attributes, and a number of data blocks?
cylinder group
Which attribute ID does NTFS set as a flag after encrypting a file where the Data Decryption Field (DDF) and Data Recovery Field (DRF) is stored?
0x100
Which cmdlet can investigators use in Windows PowerShell to analyze the GUID Partition Table data structure of the hard disk?
Get-GPT
Which cmdlet can investigators use in Windows PowerShell to analyze the GUID Partition Table to find the exact type of boot sector and display the partition object?
Get-PartitionTable
Which field type refers to the volume descriptor as a supplementary?
Number 2
Which HFS volume structure is the starting block of the volume bitmap?
Logical Block 3
Which inode field determines what the inode describes and the permissions that users have to it?
Mode
Which inode field enables the file system to correctly allow the right sort of access?
Owner Information
Which item describes the following UEFI boot process phase?The phase of EFI consisting of clearing the UEFI program from memory, transferring the UEFI program to the OS, and updating the OS calls for the run time service using a small part of the memory.
Run Time Phase
:Which of the following basic partitioning tools displays details about GPT partition tables in Linux OS?
GNU Parted
Which of the following basic partitioning tools displays details about GPT partition tables in Macintosh OS?
Disk Utility
Which of the following Federal Rules of Evidence contains Rulings on Evidence?
Rule 103
What are the five UEFI Boot Process Phases
Security Phase
Pre-EFI Initialization Phase
Driver Execution Phase
Boot Device Selection Phase
Run Time Phase
Which of the following stakeholders is responsible for conducting forensic examinations against allegations made regarding wrongdoings, found vulnerabilities, and attacks over the cloud?
Investigators
:Which of the two parts of the Linux file system architecture has the memory space where the system supplies all services through an executed system call?
Kernel Space
Which tool helps collect information about network connections operative in a Windows system?
netstat
:How many bytes does a directory entry have allotted for each file and directory in the FAT file system?
32 bytes
How many bytes is each partition entry in GPT?
128 bytes
What component of a typical FAT32 file system contains a Volume Boot Record that comprises the BIOS Parameter Block (BPB) including basic file system information, such as file system type, pointers to the position of the other sections, and the OS's boot loader code?
reserved area
What component of a typical FAT32 file system contains duplicates of the File Allocation Table to help the system check for empty or idle spaces, and contains detailed information about clusters and their contents, including files and directories?
FAT area
What information held by the superblock allows the mounting software to verify the superblock for the EXT2 file system?
Magic number
:What is a CompuServe-generated format from 1987 that uses lossless data compression techniques, maintaining the visual quality of the image?
GIF
How many bit values does HFS use to address allocation blocks?
16 bits
Which command from The Sleuth Kit (TSK) displays details of a metadata structure such as inode?
istat
On Macintosh computers, which architecture utilizes Open Firmware to initialize the hardware interfaces after the BootROM performs POST?
Power-PC
What is a common technique used to distribute malware on the web by mimicking legitimate institutions in an attempt to steal passwords, credit cards, and bank account data?
Spearphishing [Show Less]